How To Turn Off Domain_7 Search In Windows 10
This browser is no longer supported.
Upgrade to Microsoft Edge to take advantage of the latest features, security updates, and technical support.
How to observe, enable and disable SMBv1, SMBv2, and SMBv3 in Windows
Applies to: Windows Server 2022, Windows 10, Windows viii.ane, Windows 8, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, Windows Server 2012
This commodity describes how to enable and disable Server Message Block (SMB) version 1 (SMBv1), SMB version ii (SMBv2), and SMB version 3 (SMBv3) on the SMB client and server components.
While disabling or removing SMBv1 might cause some compatibility issues with one-time computers or software, SMBv1 has significant security vulnerabilities and we strongly encourage you not to use it.
Disabling SMBv2 or SMBv3 for troubleshooting
We recommend keeping SMBv2 and SMBv3 enabled, only yous might notice it useful to disable ane temporarily for troubleshooting. For more than data, see How to discover condition, enable, and disable SMB protocols on the SMB Server.
In Windows x, Windows 8.1, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2, and Windows Server 2012, disabling SMBv3 deactivates the following functionality:
- Transparent Failover - clients reconnect without pause to cluster nodes during maintenance or failover
- Scale Out - concurrent admission to shared information on all file cluster nodes
- Multichannel - assemblage of network bandwidth and fault tolerance if multiple paths are available between client and server
- SMB Direct - adds RDMA networking support for loftier performance, with low latency and depression CPU use
- Encryption - Provides end-to-stop encryption and protects from eavesdropping on untrustworthy networks
- Directory Leasing - Improves application response times in branch offices through caching
- Operation Optimizations - optimizations for small random read/write I/O
In Windows vii and Windows Server 2008 R2, disabling SMBv2 deactivates the post-obit functionality:
- Request compounding - allows for sending multiple SMBv2 requests as a single network asking
- Larger reads and writes - better use of faster networks
- Caching of folder and file properties - clients keep local copies of folders and files
- Durable handles - let for connection to transparently reconnect to the server if at that place's a temporary disconnection
- Improved bulletin signing - HMAC SHA-256 replaces MD5 as hashing algorithm
- Improved scalability for file sharing - number of users, shares, and open files per server greatly increased
- Support for symbolic links
- Client oplock leasing model - limits the data transferred betwixt the client and server, improving performance on high-latency networks and increasing SMB server scalability
- Large MTU support - for full apply of 10 Gigabit Ethernet (GbE)
- Improved energy efficiency - clients that have open files to a server can sleep
The SMBv2 protocol was introduced in Windows Vista and Windows Server 2008, while the SMBv3 protocol was introduced in Windows eight and Windows Server 2012. For more data about SMBv2 and SMBv3 capabilities, run across the following articles:
- Server Message Block overview
- What's New in SMB
How to remove SMBv1
Hither's how to remove SMBv1 in Windows 10, Windows 8.1, Windows Server 2019, Windows Server 2016, and Windows 2012 R2.
PowerShell methods
Here are the steps to detect, disable and enable SMBv1 client and server by using PowerShell commands.
Note
The computer volition restart after you lot run the PowerShell commands to disable or enable SMBv1.
-
Detect:
Get-WindowsOptionalFeature -Online -FeatureName SMB1Protocol -
Disable:
Disable-WindowsOptionalFeature -Online -FeatureName SMB1Protocol -
Enable:
Enable-WindowsOptionalFeature -Online -FeatureName SMB1Protocol
Windows Server 2012 Windows Server 2012 R2, Windows Server 2016, Windows Server 2019: Server Manager method
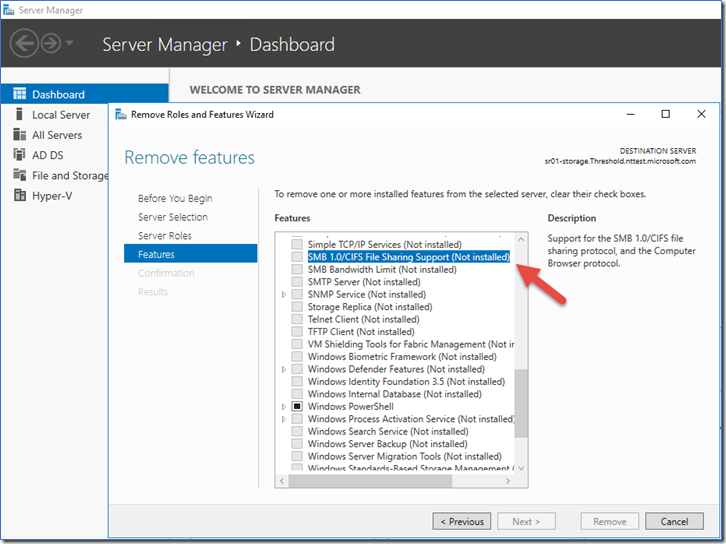
To remove SMBv1 from Windows Server:
- On the Server Manager Dashboard of the server where yous want to remove SMBv1, under Configure this local server, select Add roles and features.
- On the Earlier you begin folio, select Start the Remove Roles and Features Wizard, and then on the following page, select Next.
- On the Select destination server folio under Server Pool, ensure that the server you want to remove the characteristic from is selected, and then select Next.
- On the Remove server roles folio, select Side by side.
- On the Remove features page, clear the check box for SMB ane.0/CIFS File Sharing Support and select Side by side.
- On the Ostend removal selections page, ostend that the feature is listed, then select Remove.
Windows viii.ane and Windows 10: Add or Remove Programs method
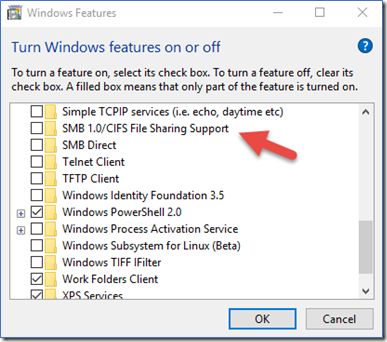
To disable SMBv1 on Windows viii.i and Windows ten:
- In Control Panel, select Programs and Features.
- Under Command Panel Domicile, select Turn Windows features on or off to open the Windows Features box.
- In the Windows Features box, scroll down the list, clear the bank check box for SMB one.0/CIFS File Sharing Back up and select OK.
- After Windows applies the change, on the confirmation page, select Restart now.
How to notice status, enable, and disable SMB protocols on the SMB Server
For Windows 8.1, Windows Server 2012, Windows Server 2012 R2, Windows 10, and Windows Server 2019
Windows 8 and Windows Server 2012 introduced the new Set-SMBServerConfiguration Windows PowerShell cmdlet. The cmdlet enables you to enable or disable the SMBv1, SMBv2, and SMBv3 protocols on the server component.
Note
When you enable or disable SMBv2 in Windows 8 or Windows Server 2012, SMBv3 is besides enabled or disabled. This behavior occurs because these protocols share the same stack.
You don't have to restart the estimator after y'all run the Gear up-SMBServerConfiguration cmdlet.
SMBv1 on SMB Server
-
Detect:
Go-SmbServerConfiguration | Select EnableSMB1Protocol -
Disable:
Set up-SmbServerConfiguration -EnableSMB1Protocol $false -
Enable:
Ready-SmbServerConfiguration -EnableSMB1Protocol $true
For more information, run into Server storage at Microsoft.
SMB v2/v3 on SMB Server
-
Find:
Get-SmbServerConfiguration | Select EnableSMB2Protocol -
Disable:
Prepare-SmbServerConfiguration -EnableSMB2Protocol $false -
Enable:
Fix-SmbServerConfiguration -EnableSMB2Protocol $true
For Windows vii, Windows Server 2008 R2, Windows Vista, and Windows Server 2008
To enable or disable SMB protocols on an SMB Server that is running Windows 7, Windows Server 2008 R2, Windows Vista, or Windows Server 2008, use Windows PowerShell or Registry Editor.
PowerShell methods
Note
This method requires PowerShell 2.0 or later version of PowerShell.
SMBv1 on SMB Server
Observe:
Go-Item HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters | ForEach-Object {Become-ItemProperty $_.pspath} Default configuration = Enabled (No registry named value is created), so no SMB1 value will be returned
Disable:
Ready-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters" SMB1 -Type DWORD -Value 0 -Force Enable:
Ready-ItemProperty -Path "HKLM:\Organisation\CurrentControlSet\Services\LanmanServer\Parameters" SMB1 -Type DWORD -Value one -Strength Note Y'all must restart the computer subsequently you make these changes. For more information, encounter Server storage at Microsoft.
SMBv2/v3 on SMB Server
Detect:
Become-ItemProperty HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters | ForEach-Object {Get-ItemProperty $_.pspath} Disable:
Set-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters" SMB2 -Type DWORD -Value 0 -Force Enable:
Set-ItemProperty -Path "HKLM:\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters" SMB2 -Type DWORD -Value ane -Strength Note
You must restart the computer after you lot make these changes.
Registry Editor
Important
Follow the steps in this section advisedly. Serious issues might occur if you modify the registry incorrectly. Before yous modify it, back up the registry for restoration in example problems occur.
To enable or disable SMBv1 on the SMB server, configure the post-obit registry key:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters
Registry entry: SMB1 REG_DWORD: 0 = Disabled REG_DWORD: i = Enabled Default: 1 = Enabled (No registry central is created) To enable or disable SMBv2 on the SMB server, configure the following registry key:
HKEY_LOCAL_MACHINE\System\CurrentControlSet\Services\LanmanServer\Parameters
Registry entry: SMB2 REG_DWORD: 0 = Disabled REG_DWORD: 1 = Enabled Default: 1 = Enabled (No registry fundamental is created) Notation
You must restart the reckoner afterwards y'all make these changes.
How to detect status, enable, and disable SMB protocols on the SMB Client
Here is how to detect status, enable, and disable SMB protocols on the SMB Client that is running Windows ten, Windows Server 2019, Windows 8.1, Windows Server 2016, Windows Server 2012 R2, and Windows Server 2012.
Note
When you enable or disable SMBv2 in Windows 8 or in Windows Server 2012, SMBv3 is also enabled or disabled. This behavior occurs considering these protocols share the same stack.
SMBv1 on SMB Customer
-
Observe
sc.exe qc lanmanworkstation -
Disable:
sc.exe config lanmanworkstation depend= bowser/mrxsmb20/nsi sc.exe config mrxsmb10 showtime= disabled -
Enable:
sc.exe config lanmanworkstation depend= bowser/mrxsmb10/mrxsmb20/nsi sc.exe config mrxsmb10 start= auto
For more information, run into Server storage at Microsoft
SMBv2/v3 on SMB Client
-
Detect:
sc.exe qc lanmanworkstation -
Disable:
sc.exe config lanmanworkstation depend= bowser/mrxsmb10/nsi sc.exe config mrxsmb20 start= disabled -
Enable:
sc.exe config lanmanworkstation depend= bowser/mrxsmb10/mrxsmb20/nsi sc.exe config mrxsmb20 start= auto
Note
- You must run these commands at an elevated command prompt.
- You must restart the computer after you make these changes.
Disable SMBv1 by using Group Policy
This department introduces how to use Group Policy to disable SMBv1. You can use this method on different versions of Windows.
Disable SMBv1 server
This process configures the post-obit new item in the registry:
HKEY_LOCAL_MACHINE\Arrangement\CurrentControlSet\Services\LanmanServer\Parameters
- Registry entry: SMB1
- REG_DWORD: 0 = Disabled
To use Group Policy to configure this, follow these steps:
-
Open up the Group Policy Direction Console. Correct-click the Grouping Policy object (GPO) that should incorporate the new preference item, and and so click Edit.
-
In the console tree under Computer Configuration, aggrandize the Preferences folder, and then expand the Windows Settings folder.
-
Right-click the Registry node, point to New, and select Registry Item.
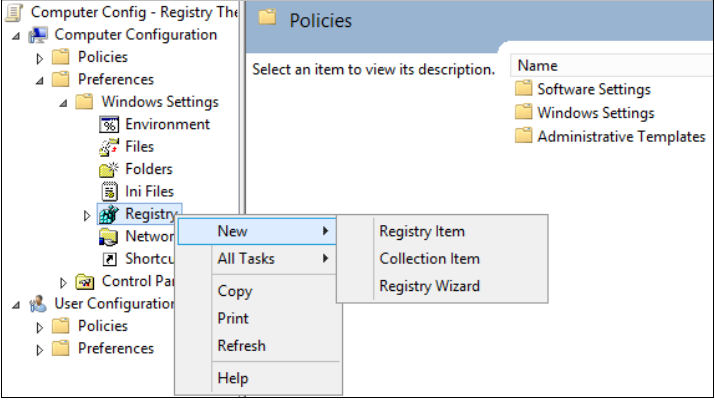
In the New Registry Properties dialog box, select the following:
- Action: Update
- Hive: HKEY_LOCAL_MACHINE
- Fundamental Path: SYSTEM\CurrentControlSet\Services\LanmanServer\Parameters
- Value name: SMB1
- Value blazon: REG_DWORD
- Value data: 0

This procedure disables the SMBv1 Server components. This Grouping Policy must be applied to all necessary workstations, servers, and domain controllers in the domain.
Annotation
WMI filters can also be gear up to exclude unsupported operating systems or selected exclusions, such as Windows XP.
Important
Exist conscientious when you make these changes on domain controllers on which legacy Windows XP or older Linux and 3rd-political party systems (that don't support SMBv2 or SMBv3) require admission to SYSVOL or other file shares where SMB v1 is being disabled.
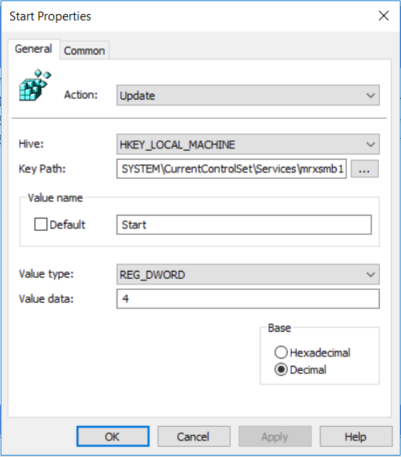
Disable SMBv1 client
To disable the SMBv1 client, the services registry cardinal needs to exist updated to disable the get-go of MRxSMB10 and and then the dependency on MRxSMB10 needs to exist removed from the entry for LanmanWorkstation so that information technology can outset usually without requiring MRxSMB10 to beginning start.
This guidance updates and replaces the default values in the following two items in the registry:
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\services\mrxsmb10
Registry entry: Showtime REG_DWORD: four= Disabled
HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\LanmanWorkstation
Registry entry: DependOnService REG_MULTI_SZ: "Bowser","MRxSmb20″,"NSI"
Notation
The default included MRxSMB10 which is now removed as dependency.
To configure this by using Group Policy, follow these steps:
-
Open the Grouping Policy Direction Console. Right-click the GPO that should contain the new preference item, and so click Edit.
-
In the console tree under Computer Configuration, expand the Preferences binder, and and so expand the Windows Settings folder.
-
Right-click the Registry node, point to New, and select Registry Item.
-
In the New Registry Backdrop dialog box, select the following:
- Action: Update
- Hive: HKEY_LOCAL_MACHINE
- Key Path: SYSTEM\CurrentControlSet\services\mrxsmb10
- Value name: Start
- Value type: REG_DWORD
- Value data: 4
-
And so remove the dependency on the MRxSMB10 that was disabled.
In the New Registry Properties dialog box, select the following:
- Action: Supervene upon
- Hive: HKEY_LOCAL_MACHINE
- Key Path: SYSTEM\CurrentControlSet\Services\LanmanWorkstation
- Value name: DependOnService
- Value type: REG_MULTI_SZ
- Value information:
- Bowser
- MRxSmb20
- NSI
Note
These three strings will not have bullets (run into the following screen shot).
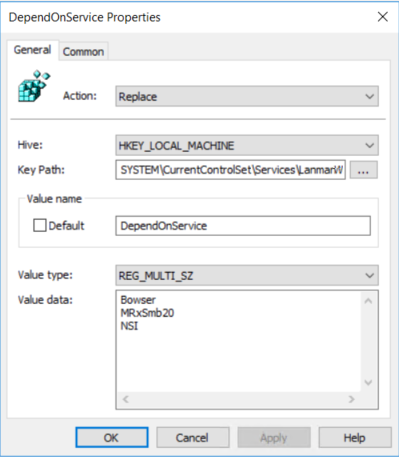
The default value includes MRxSMB10 in many versions of Windows, and so by replacing them with this multi-value string, information technology is in effect removing MRxSMB10 as a dependency for LanmanWorkstation and going from four default values down to just these three values above.
Note
When yous use Group Policy Management Panel, y'all don't accept to use quotation marks or commas. Only type each entry on individual lines.
-
Restart the targeted systems to cease disabling SMB v1.
Auditing SMBv1 usage
To decide which clients are attempting to connect to an SMB server with SMBv1, you lot can enable auditing on Windows Server 2016, Windows 10, and Windows Server 2019. Y'all can also audit on Windows seven and Windows Server 2008 R2 if the May 2018 monthly update is installed, and on Windows 8.one and Windows Server 2012 R2 if the July 2017 monthly update is installed.
-
Enable:
Ready-SmbServerConfiguration -AuditSmb1Access $true -
Disable:
Set-SmbServerConfiguration -AuditSmb1Access $imitation -
Observe:
Get-SmbServerConfiguration | Select AuditSmb1Access
When SMBv1 auditing is enabled, event 3000 appears in the "Microsoft-Windows-SMBServer\Audit" event log, identifying each client that attempts to connect with SMBv1.
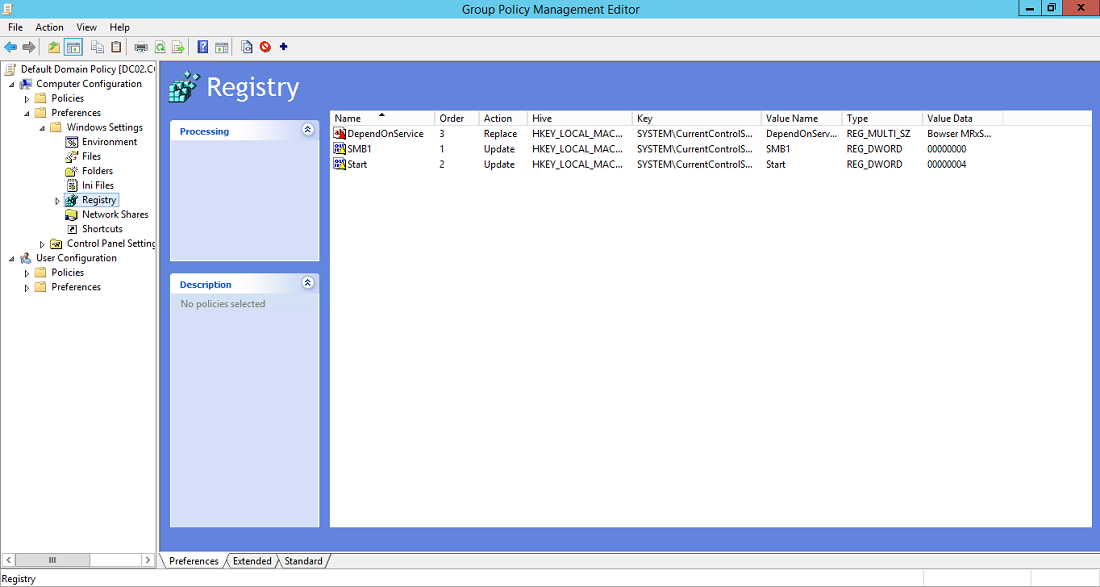
Summary
If all the settings are in the same GPO, Group Policy Management displays the post-obit settings.
Testing and validation
Later on completing the configuration steps in this article, allow the policy to replicate and update. As necessary for testing, run gpupdate /force at a command prompt, and then review the target computers to make sure that the registry settings are applied correctly. Make sure SMBv2 and SMBv3 are operation for all other systems in the surround.
Note
Don't forget to restart the target systems.
Feedback
Submit and view feedback for
Source: https://docs.microsoft.com/en-us/windows-server/storage/file-server/troubleshoot/detect-enable-and-disable-smbv1-v2-v3
Posted by: lemenmaress61.blogspot.com

0 Response to "How To Turn Off Domain_7 Search In Windows 10"
Post a Comment