How To Enable Integrated Windows Authentication In Chrome
Configuring Chrome and Firefox for Windows Integrated Authentication
(Last updated on November 5, 2021)
Windows Integrated Authentication allows a users' Agile Directory credentials to pass through their browser to a web server. Windows Integrated Hallmark is enabled by default for Internet Explorer but not Google Chrome or Mozilla Firefox. Users who utilise the non-Microsoft browsers will receive a pop-upward box to enter their Active Directory credentials earlier continuing to the website. This adds additional steps and complexity for users who are using web based applications like self-service countersign reset solutions Specops uReset and Specops Password Reset. In an effort to make this process every bit easy equally possible for end-users, many IT administrators enable Windows Integrated Hallmark for the 3rd party browsers. This can be washed with Chrome and Firefox with a few boosted steps. This article will evidence yous how to enable Windows Integrated Authentication for Google Chrome and Mozilla Firefox.
Configuring Delegated Security for Mozilla Firefox
To configure Firefox to use Windows Integrated Authentication:
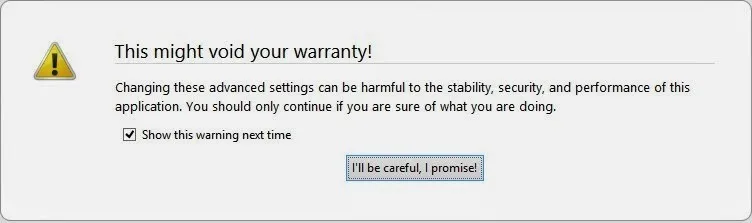
1. Open Firefox.
2. In the address bar type nigh:config
3. You will receive a security alert. To go along, click I'll be careful, I promise.
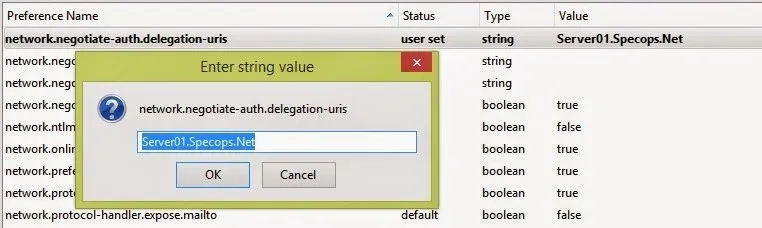
4. You will run across a list of preferences listed. Detect the settings below past browsing through the listing or searching for them in the search box. Once you accept located each setting, update the value to the post-obit:
| Setting | Value |
|---|---|
| network.automatic-ntlm-auth.trusted-uris | MyIISServer.domain.com |
| network.automatic-ntlm-auth.let-proxies | True |
| network.negotiate-auth.permit-proxies | True |
** MyIISServer.domain.com should be the fully qualified name of your IIS server that you are setting up the Windows Integrated Hallmark to.
Negotiate authentication is not supported in versions of Firefox prior to 2006.
![]()
Configuring Delegated Security in Google Chrome
Note: The latest version of Chrome uses existing Internet Explorer settings. Older version of Chrome require additional configurations (run across below).
Yous can apply three methods to enable Chrome to use Windows Integrated Authentication.Your options are the command line, editing the registry, or using ADMX templates through group policy. If y'all choose to employ the command line or edit the registry, you could use Group Policy Preferences to distribute those changes on a broader scale. Below are the steps for the iii methods:
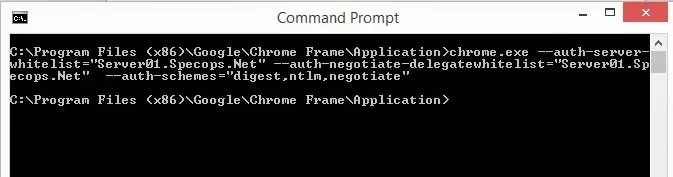
To utilise the command line to configure Google Chrome
Get-go Chrome with the following command:
Chrome.exe –auth-server-whitelist="MYIISSERVER.DOMAIN.COM" –auth-negotiate-delegatewhitelist="MYIISSERVER.DOMAIN.COM" –auth-schemes="digest,ntlm,negotiate"
To modify the registry to configure Google Chrome
Configure the following registry settings with the corresponding values:
Registry
AuthSchemes
Information blazon: String (REG_SZ)
Windows registry location:Software\Policies\Google\Chrome\AuthSchemes
Mac/Linux preference name : AuthSchemes
Supported on: Google Chrome (Linux, Mac, Windows) since version 9
Supported features: Dynamic Policy Refresh: No, Per Profile: No
Description: Specifies which HTTP Hallmark schemes are supported by Google Chrome. Possible values are 'basic', 'digest', 'ntlm'and 'negotiate'. Separate multiple values with commas. If this policy is left not set, all four schemes volition be used.
Value: "basic,digest,ntlm,negotiate"
AuthServerWhitelist
Information type: String (REG_SZ)
Windows registry location : Software\Policies\Google\Chrome\AuthServerWhitelist
Mac/Linux preference proper name : AuthServerWhitelist
Supported on : Google Chrome (Linux, Mac, Windows) since version ix
Supported features : Dynamic Policy Refresh: No, Per Contour: No
Description : Specifies which servers should exist whitelisted for integratedhallmark. Integrated authentication is only enabled when Google Chrome receives an authentication challenge from a proxy or from a server which is in this permitted list. Separate multiple server names with commas. Wildcards (*) are allowed. If you exit this policy not set Chrome will try to find if a server is on the Intranet and only and then will information technology respond to IWA requests. If a server is detected as Internet and then IWA requests from it will be ignored by Chrome.
Value: "MYIISSERVER.DOMAIN.COM"
AuthNegotiateDelegateWhitelist
Information type: String (REG_SZ)
Windows registry location : Software\Policies\Google\Chrome\AuthNegotiateDelegateWhitelist
Mac/Linux preference name : AuthNegotiateDelegateWhitelist
Supported on : Google Chrome (Linux, Mac, Windows) since version 9
Supported features : Dynamic Policy Refresh: No, Per Profile: No
Description: Servers that Google Chrome may delegate to. Separate multiple server names with commas. Wildcards (*) are immune. If y'all exit this policy not set Chrome will not delegate user credentials fifty-fifty if a server is detected equally Intranet.
Example Value: "MYIISSERVER.DOMAIN.COM"
To use ADM/ADMX templates through Group Policy to configure Google Chrome
one. Download Null file of ADM/ADMX templates and documentation from: http://www.chromium.org/administrators/policy-templates.
two. Add together the ADMX template to your central store, if y'all are using a primal store.
3. Configure a GPO with your application server DNS host name with Kerberos Delegation Server Whitelistand Authentication Server Whitelistenabled.
Each of these three methods attain the same results for configuring Google Chrome for Windows Integrated Authentication. The method that is best for you will depend on how your organization is set up. Personally, I would utilize the control line or the registry if you are deploying across an enterprise. You lot tin can easily distribute a shortcut on the user's desktop with the command and distribute that with Group Policy preferences. If yous cull to use the registry method, that is able to exist distributed with Grouping Policy.
With a variety of third-party browsers available, many users will receive a pop-up box to enter their Active Directory credentials before continuing to an IIS hosted web application. This leads to additional steps, complexity and confusion for many end-users. Past setting upwardly Windows Integrated Authentication into Chrome and Firefox, y'all will exist able to requite your users the greatest corporeality of flexibility for their choice of browser too as ease of apply with your web-based applications.
Making everyday IT tasks easier for end users and IT admins is something we specialize in. Our self-service password reset solution Specops uReset guarantees finish user adoption thanks to its flexible approach to multi-gene hallmark.
Source: https://specopssoft.com/blog/configuring-chrome-and-firefox-for-windows-integrated-authentication/
Posted by: lemenmaress61.blogspot.com

0 Response to "How To Enable Integrated Windows Authentication In Chrome"
Post a Comment